Forensic Imaging and Collections
Each matter is unique. Our consultants will assist you in determining which collection methodology, or combinations thereof, will be the most appropriate and cost-effective solution given the variables you are presented with.
Forensic Collections
When it comes to cases today, virtually all forms of electronic data can be considered fair game. Even though counsel and the internal IT team have identified and preserved the data, it still needs to be collected. Depending on the data source, the technical expertise and forensic capabilities needed to properly collect the data vary drastically based upon the accessibility and complexity of the data.
On-Site Collections Forensics
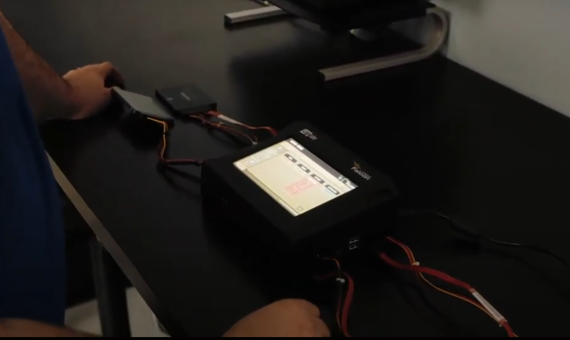
On-site collections are advisable when full forensic images of electronic devices are needed, when there are dozens or even hundreds of custodian workstations and mobile devices at a location, or when the pertinent data is contained in a highly complex IT environment.
Our experts are equipped with leading forensic imaging technology solutions that allow for rapid deployment and acquisition of the data in question. If there is a narrow window of time in which all relevant data must be acquired, we can provide as many experts as needed for an on-site collection. All of our experts who handle forensic collections possess numerous certifications in computer and mobile forensics, so you can be assured that the collections will be done in accordance with forensic best practices and will be defensible in court.
Remote Collections Forensics
Remote collections can provide significant cost and time savings for an organization, especially if collections are to be performed over an extended period of time as relevant data is identified. With more employees working remotely today than ever before, remote collections are critical in addressing the unique challenges of data collection for a distributed workforce.
Our experts have the experience and technological solutions to quickly and effectively acquire and preserve data from employee computers, file shares, email, and cloud data. These collections, which can run in the background and be performed after hours for surgical precision in collecting specific data, allow for as many collections as needed from the custodian. Our experts ensure that the remote collection process is forensically sound and therefore defensible.
Hybrid Data Collections Forensics
Hybrid collections are an option for many collections, as the same matter often has some data that is best collected on-site and other data that can be collected remotely over time. Our experts can perform the necessary on-site collections and set up forensic technology solutions at a location in order to collect data remotely with minimal disruption to the organization and its employees.
In-Lab Data Collections Forensics
In-lab collections should be performed when possible. Clients commonly choose to ship or deliver electronic devices to one of our forensic labs for collection. This method is highly cost-effective, as no travel fees or expenses are incurred. It can also be the least intrusive on schedules. When a custodian can be without a device during the collection process, this method has many benefits. By working closely with our clients, our experts can schedule these collections to begin upon arrival of the devices or close to it, allowing for the quickest possible turnaround time.
Types of Data Collection Forensics
Active Data Collections Forensics
Active data is the data that users access and use regularly. This data includes files that are stored locally on the internal hard drives of laptops and computers, external storage media, and data contained on network drives. Our experts have a broad array of software and hardware solutions to create full forensic images of devices and perform targeted logical collections.
Mobile Data Collections Forensics
Collecting data in a forensically sound manner from mobile devices, such as mobile phones and tablets, requires highly specialized forensic tools and typically requires the use of a digital forensic expert to perform the extraction and preservation of data. There are thousands of forensic artifacts recoverable from mobile devices, including call logs, text messages, application-based instant messaging, geolocation data, searches, and internet history.
Cloud Data Collections Forensics
Our experts are experienced in collecting data from internal, external, and hybrid cloud environments. Whether the cloud is behind a firewall in a private enterprise, hosted by Google, Amazon, or Microsoft, we have the expertise and forensic technology to collect the electronic information. Further, data contained on social media networks like Facebook, Twitter, LinkedIn, Instagram, and others, can be both collected and actively monitored by forensic software to auto-collect and preserve new data as it is created.
Offline Data Collections Forensics
Offline sources of data typically include computers, mobile phones, external storage media, and servers that have been taken offline and are in storage. The forensic collection of these devices is typically not overly complicated as long as the enterprise knows its physical location. Our experts are available to perform the forensic acquisition of these devices onsite or at one of our forensic labs if the devices are picked up or dropped off.
Backup Data Collections Forensics
Data contained on traditional backup solutions, including tapes, antiquated hard drives, and disks, can pose technical challenges and be one of the most complex scenarios in forensic data collection. The challenges stem from acquiring the necessary hardware devices to read the media and copies of proprietary software programs to view it. We maintain many of these old tape and disk readers, hardware devices, and software programs at our facilities to address these challenges.
Hidden Data Collection Forensics
Fragmented data or data that was previously deleted from devices constitute the majority of hidden sources. As digital forensics experts, we are highly skilled and equipped to recover deleted and fragmented data that is not accessible to users and IT personnel. Another form of hidden sources can include the use of software programs to hide data, which we can analyze devices for. There are also anti-forensic tools used to truly delete data, which our experts are highly familiar with through testing and case experience. In almost every instance, if one of these anti-forensic tools was utilized, it would leave tracks that can be found.
Structured Data Collection Forensics
Spreadsheets, databases, and accounting information systems are all examples of structured data, a class of data with a reliable and consistent structure. All other forms of data, such as messaging, emails, social media, and other types of web based-content, are unstructured data. Our team has the ability to pull reports from structured data locations and has consulted on many matters involving this form of electronically stored information.
The Envista Difference: Forensic Collections Forensics
Forensic collections are more complicated today than ever before, and the rapidly advancing pace of technology will ensure it continues to be a highly complex field. At Envista, we anticipate future complexities so we can meet tomorrow's challenges. At the core, our strength is in our experts. In a single matter, data can be contained in computers, mobile devices, the cloud, and complex network environments. Through continual training and development, our team can serve on the front line for all forms of data collection, all done according to industry standards and digital forensic best practices to provide our clients with the strongest defensible position.
Please fill out the form below to let us know!